Spam Verification Insight Hub Spam Number Checker Explaining Caller Validation Searches
Spam Verification Insight Hub’s approach to Spam Number Checking frames caller validation as a real-time risk assessment. It consolidates signals from multiple data sources into a coherent trust score. The method emphasizes disciplined data handling and timely updates to maintain accuracy. It translates diverse indicators into actionable judgments, guiding blocking and trusted-call designations. The framework invites scrutiny of evolving reputation signals and their ethical application, leaving readers curious about how these tools perform in practice.
What Is Spam Number Checking and Why It Matters
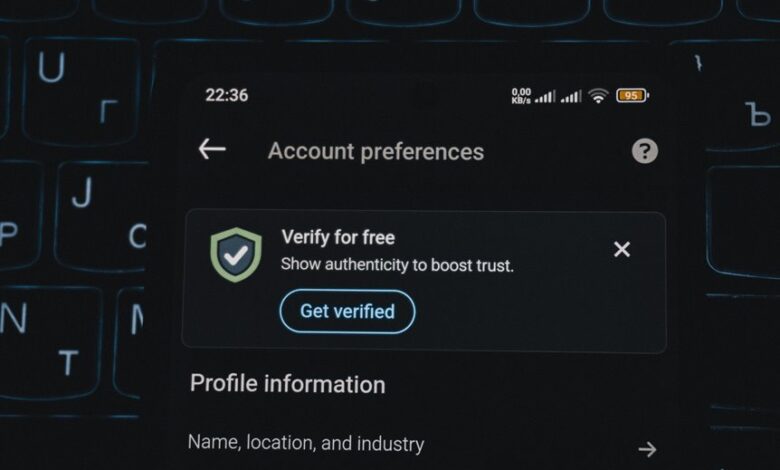
Spam number checking is the process of evaluating phone numbers to determine whether they are associated with unwanted or fraudulent activity. The goal is transparency and protection, enabling informed choices. This practice supports spam detection and strengthens caller authentication, reducing risk for individuals and organizations. Implementations emphasize reliability, data quality, and ethical handling to maintain user freedom and trust. spam detection, caller authentication, two word ideas: breach shield, fraud guard
How Caller Validation Searches Work in Real Time
Real-time caller validation searches integrate multiple data sources and algorithms to assess a phone number’s current risk profile as a call occurs. They harness real time signals, feed verification workflows, and update caller reputation scores. Telephony analytics synthesize indicators into a concise risk assessment, revealing Spam truth and enabling proactive blocking, filtering, and trusted caller designation with clarity and precision.
How to Interpret Verification Signals for Calls
Interpreting verification signals for calls requires translating diverse indicators into actionable risk assessments. The analysis centers on verification signals, along with caller validation metrics, spam data, and real time checks. Clear categorization distinguishes benign from suspicious patterns, enabling timely decisions. Structured evaluation balances context, frequency, and source credibility, supporting informed risk management while preserving user autonomy and freedom in communication choices.
Practical Tips to Improve Your Spam Verification Results
Effective spam verification results hinge on disciplined data handling and methodical checks. The discussion presents practical tips for refining processes, emphasizing consistent data sources, rigorous cross-checking, and timely updates. It outlines how to interpret verification signals, avoid false positives, and document decisions. A disciplined workflow enhances transparency, reproducibility, and trust, empowering users seeking freedom to assess caller legitimacy efficiently.
Conclusion
The hub’s framework quietly gathers signals, stitching them into a single, evolving score. As data streams converge, trust and threat edge closer, yet never settle. Each real-time update reframes the caller’s identity, shifting the balance between safety and risk. Readers are left anticipating the next refinement, the next data point that could alter fate. In this careful, disciplined process, what is trusted today may be reassessed tomorrow, keeping vigilance—and suspense—ever present in the pursuit of clean verification.






