Phone Verification Research Hub Robocall Phone Number Lookup Explaining Scam Detection Searches
The topic centers on how a Phone Verification Research Hub combines robocall risk assessment with phone-number lookups to explain scam-detection searches. It emphasizes modular, auditable workflows that synthesize telemetry and cross-source signals into risk scores. The approach aims for reproducibility and privacy-conscious verification, supported by independent checks and caller-ID validation. The framework retains unverified-caller flags and documents uncertainty, offering a structured basis for ongoing risk comparison, while hinting at unresolved challenges that warrant further scrutiny.
What Is Robocall Risk and How Phone Lookups Help
Robocall risk refers to the probability that an automated telephone call will deliver a fraudulent or harmful message, typically characterized by spoofed caller IDs, high-volume outgoing attempts, and scripted content designed to elicit personal or financial information.
Rigorous assessment combines signal analysis, network provenance, and behavioral metrics.
Phone lookups provide contextual validation, enabling resilient filtering and informed decision-making against anomalous call patterns without restricting freedom.
robocall risk remains measurable.
How Scam-Detection Searches Work in Practice
How scam-detection searches operate in practice involve a disciplined sequence of data acquisition, feature extraction, and evidence synthesis. In this framework, scam detection workflows aggregate telemetry and caller id analytics to form risk scores, supporting comparative assessments across sources. Systematic validation underpins reliability, while modular pipelines enable rapid updates. The approach emphasizes transparency, reproducibility, and disciplined skepticism toward automated labeling and inherent biases.
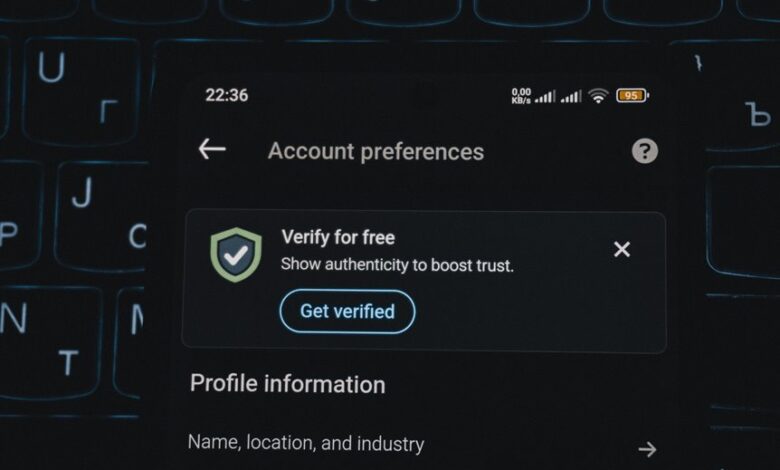
Practical Steps to Verify a Caller Before Answering
Practical steps to verify a caller before answering involve a structured, evidence-based protocol that minimizes exposure to potentially fraudulent calls. The procedure emphasizes independent cross-checks, caller ID verification, and caller-supplied context. A risk assessment remains essential when information is incomplete, guiding whether to engage further. An unverified caller warrants heightened scrutiny, documenting flags and delaying disclosure until corroborated evidence exists.
Choosing Tools and Best Practices for Ongoing Protection
To maintain resilience against evolving scam tactics, ongoing protection relies on a calibrated mix of tools and disciplined practices. The discussion emphasizes reproducible workflows, provenance, and transparent validation of signals from robocall lookups.
Emphasis is placed on privacy metrics and data governance when aggregating telemetry, balancing detection sensitivity with user autonomy. Decisions favor auditable, modular architectures over opaque, monolithic systems.
Conclusion
In rigorous contrast, the system’s structured, auditable pipeline stands beside the unpredictable noise of unsolicited calls. Quantified risk scores and independent verifications provide objective ballast where caller intent remains opaque. Practical verification steps juxtapose theory with real-world friction, highlighting privacy-preserving safeguards alongside pressure points of false positives. Thus, data-driven telemetry coexists with user autonomy, enabling resilient protection while acknowledging residual uncertainty inherent in robotic and human actors.






