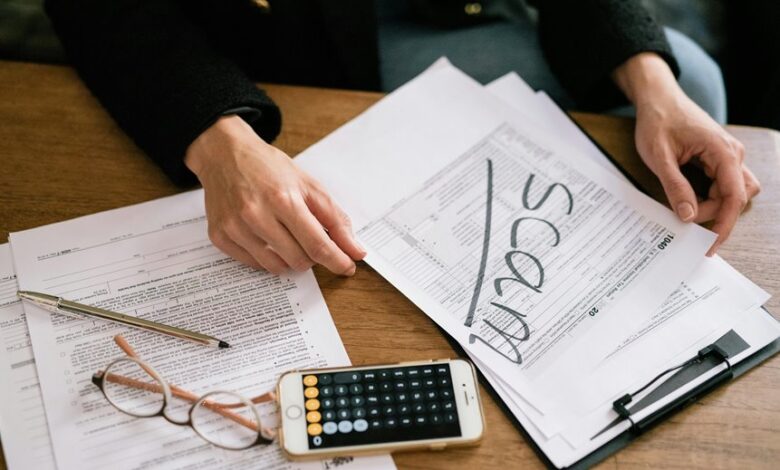
Scam Investigation Insight Portal Scam Phone Number Lookup Revealing Caller Identification
The Scam Investigation Insight Portal’s phone-number lookup aggregates public registries, carrier signals, and user input to identify callers. Analysts triangulate data with reputable scam sources to produce a concise risk profile. The approach emphasizes transparency, auditability, and user autonomy, allowing verification from independent sources. It flags high-risk numbers and supports informed decisions, yet leaves room for further scrutiny as new data emerge. This balance invites scrutiny of the methodology and its real-world limits.
What the Scam Investigation Insight Portal Does for You
The Scam Investigation Insight Portal systematically aggregates caller data from multiple sources to identify patterns and flag high-risk numbers. It translates raw signals into actionable insights, enabling users to verify legitimacy and avoid scams. Leveraging scam analytics and refined caller intelligence, the system supports informed decisions, promotes personal autonomy, and reduces risk without compromising privacy or freedom.
How a Scam Phone Number Lookup Works
A systematic workflow underpins a scam phone number lookup, building on the broad data aggregation described earlier. The process integrates verified caller data, cross-referenced with reputable scam research sources, to construct a concise risk profile.
Analysts corroborate outcomes by triangulating databases, call patterns, and reported incidents, ensuring transparency while preserving user autonomy and freedom from manipulation.
Reading Caller Identification: Data Sources and Reliability
Reading caller identification hinges on evaluating multiple data streams for credibility and completeness. The analysis focuses on reading data from public registries, carrier signals, and user-contributed inputs, weighed against independent verification and recency. Caller sources reliability varies by jurisdiction and update cadence; triangulation reduces error. A disciplined approach emphasizes transparency, auditability, and ongoing verification to preserve user autonomy in a free information landscape.
Spotting Red Flags and Verifying Numbers in Practice
Could red flags emerge quickly when numbers surface across disparate data feeds, or do they require careful corroboration? In practice, analysts compare multiple data sources, identify scam indicators, and map consistent patterns. Verification steps include cross-checking call metadata, source reputations, and recent reports. Red flags arise from unusual timing, spoofing, or inconsistent caller IDs, while corroborated data strengthens conclusions beyond isolated entries.
Conclusion
The Scam Investigation Insight Portal promises clarity by collating data from public registries, carriers, and user inputs, then producing a tidy risk profile. Ironically, its rigor rests on triangulation—yet users are urged to verify independently. Analysts label numbers with precision, while still acknowledging uncertainty. In practice, the system provides an orderly map through noisy signals, enabling informed decisions. Ultimately, transparency and auditability triumph, even as one remains cautiously skeptical about every variable beneath the surface.






